Compromised identities are now the #1 entry point for breaches.
But all we have are disconnected alerts – endpoint signals in one tool, identity risks in another, and third-party threat data somewhere else entirely.
By the time you piece it all together, the attacker has already moved.
𝐔𝐧𝐢𝐟𝐢𝐞𝐝 𝐑𝐢𝐬𝐤 𝐒𝐢𝐠𝐧𝐚𝐥𝐬 (𝐜𝐮𝐫𝐫𝐞𝐧𝐭𝐥𝐲 𝐢𝐧 𝐏𝐫𝐞𝐯𝐢𝐞𝐰) brings it all together.
Here’s what comes with it:
🔗 𝐂𝐫𝐨𝐬𝐬-𝐩𝐥𝐚𝐭𝐟𝐨𝐫𝐦 𝐬𝐢𝐠𝐧𝐚𝐥 𝐚𝐠𝐠𝐫𝐞𝐠𝐚𝐭𝐢𝐨𝐧 — Microsoft Defender + non-Microsoft sources unified in one score
🎯 𝐀𝐮𝐭𝐨𝐦𝐚𝐭𝐢𝐜 𝐂𝐨𝐧𝐝𝐢𝐭𝐢𝐨𝐧𝐚𝐥 𝐀𝐜𝐜𝐞𝐬𝐬 — When the score rises, your Conditional Access policies respond automatically
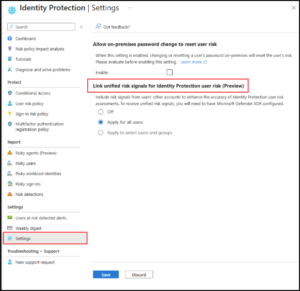
📊 𝐑𝐢𝐬𝐤𝐲 𝐔𝐬𝐞𝐫 𝐑𝐞𝐩𝐨𝐫𝐭 — full risk details and Identity Risk Score in one view ⚙️ 𝐅𝐥𝐞𝐱𝐢𝐛𝐥𝐞 𝐜𝐨𝐧𝐟𝐢𝐠𝐮𝐫𝐚𝐭𝐢𝐨𝐧 — enable for all users or target specific groups
📍 To get started: 𝘌𝘯𝘵𝘳𝘢 𝘈𝘥𝘮𝘪𝘯 𝘊𝘦𝘯𝘵𝘦𝘳 → 𝘐𝘋 𝘗𝘳𝘰𝘵𝘦𝘤𝘵𝘪𝘰𝘯 → 𝘋𝘢𝘴𝘩𝘣𝘰𝘢𝘳𝘥 → 𝘚𝘦𝘵𝘵𝘪𝘯𝘨𝘴 → 𝘌𝘯𝘢𝘣𝘭𝘦 𝘜𝘯𝘪𝘧𝘪𝘦𝘥 𝘙𝘪𝘴𝘬 𝘚𝘪𝘨𝘯𝘢𝘭𝘴
Identity is your most attacked surface. It’s time your risk signals matched that reality.