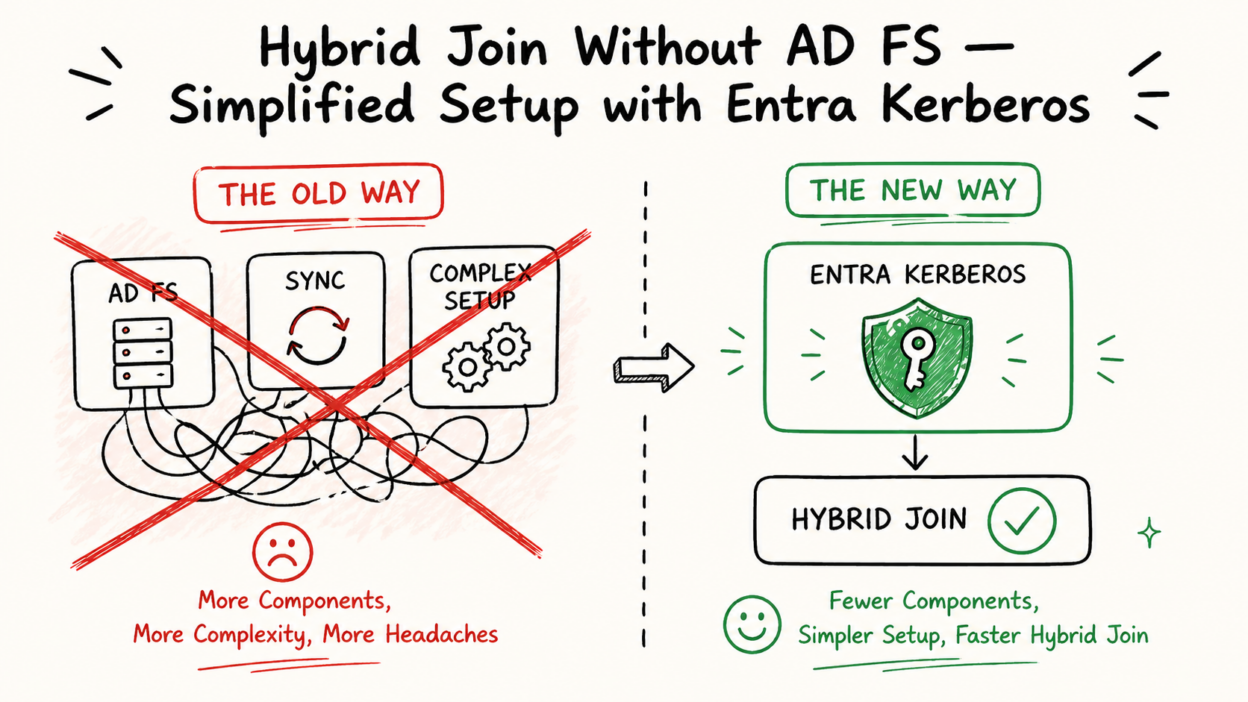
Most hybrid join implementations don’t struggle because the capability isn’t there; they struggle because the architecture becomes too heavy to manage. AD FS dependencies, sync requirements, and tightly coupled components often turn what should be a straightforward setup into a prolonged, high-effort project.
Microsoft Entra Kerberos Hybrid Join
This preview capability shifts that model. With Microsoft Entra Kerberos–based hybrid join, devices can be registered across on-prem AD and Entra ID without relying on AD FS or Microsoft Entra Connect Sync. That’s a meaningful change in how hybrid identity can be approached.
Where this stands out most is in environments that traditionally face friction: VDI deployments, disconnected forests, and Azure Virtual Desktop scenarios —
places where Connect Sync hasn’t always been practical.
places where Connect Sync hasn’t always been practical.
From an architectural perspective, the benefits are clear: it reduces reliance on legacy federation layers, simplifies identity flows for modern, cloud-aligned environments, and enables faster provisioning, especially for VDI and cloud desktops. That said, this isn’t simplification without trade-offs.
That said, this isn’t simplification without trade-offs. It introduces a different kind of constraint —strict dependency on newer infrastructure (Windows Server 2025, updated Windows 11 builds).
So the more relevant question becomes: Is your environment ready to support this model?
- If your organization is already moving toward a modern identity stack, this is a strong direction to evaluate.
- If not, this serves as an early indicator of where hybrid identity is heading —and what your roadmap will eventually need to accommodate.