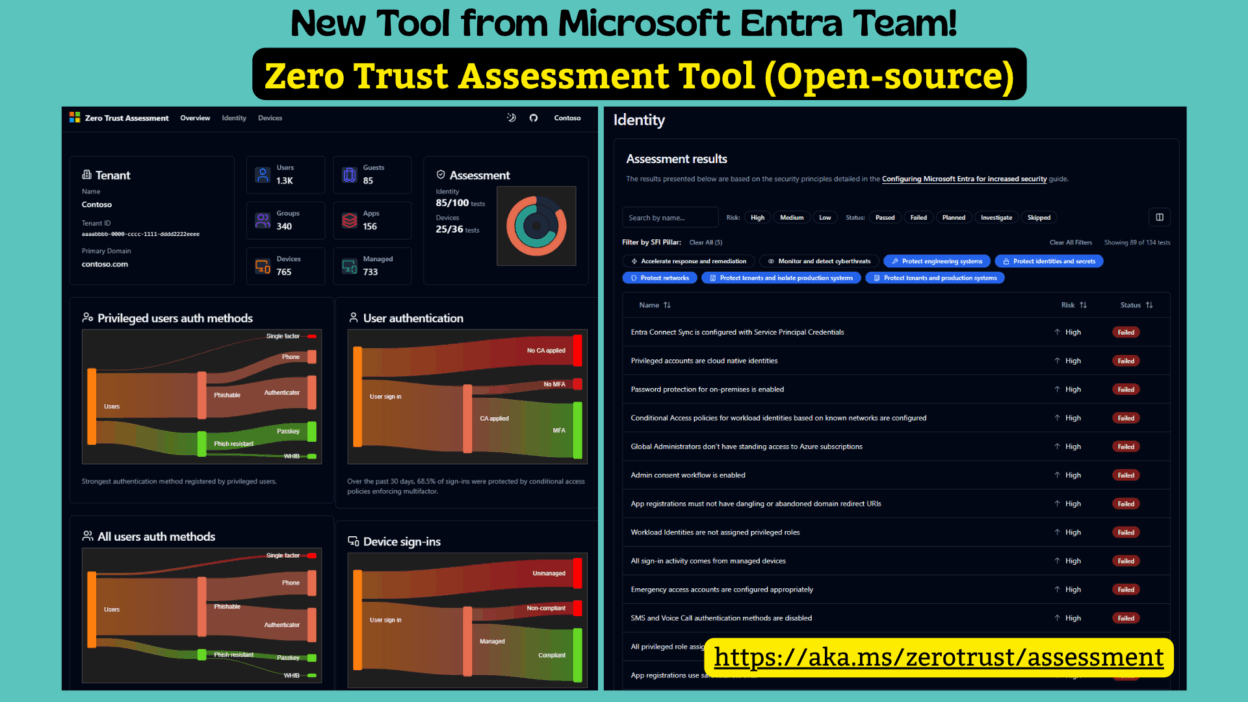
Saw a new tool announcement from the Microsoft Entra team. They’ve launched an 𝐨𝐩𝐞𝐧-𝐬𝐨𝐮𝐫𝐜𝐞 𝐙𝐞𝐫𝐨 𝐓𝐫𝐮𝐬𝐭 𝐀𝐬𝐬𝐞𝐬𝐬𝐦𝐞𝐧𝐭 𝐭𝐨𝐨𝐥.
- Basically, a simple way to review and understand your security posture.
- It reviews your Identity and Device configurations and then hands you a report & dashboards showing what’s secure, what’s weak, and what to fix first.
- The tests aren’t arbitrary either; they pull from well-known standards👏🏻 like NIST, CISA, CIS, Microsoft’s own internal baselines, and insights from real customer environments.
So the recommendations feel grounded in practical reality, not theory.
What caught my attention is the simplicity! Zero Trust often feels huge in theory, but this makes it more actionable. We can easily get risk levels, user impact, and effort required, which is a lot more useful than another checklist.
The workflow is pretty minimal, too. Just install the module, connect, run the assessment, and review the findings:
First, you install the ZeroTrustAssessment PowerShell module.
Install-Module ZeroTrustAssessment -Scope CurrentUser
Then, you connect to Microsoft Graph and to Azure by signing into your tenant.
Connect-ZtAssessment
After that, you run one command to start the data collection. For larger tenants, this step can take a few hours.
Invoke-ZtAssessment
It only uses read-only permissions and runs the analysis locally, but keep in mind the output is sensitive, so treat it like any other high-risk security artifact.
Simple enough to start, but structured enough to guide a meaningful cleanup.
If you want to try it, here’s the link: https://learn.microsoft.com/en-us/security/zero-trust/assessment/overview