PowerShell remains one of the most powerful and essential tools for Microsoft 365 administration. However, this immense power inherently carries significant security risks. The reality is that a compromised admin account with unrestricted PowerShell access can lead to catastrophic data breaches, sweeping configuration changes, or a complete tenant takeover.
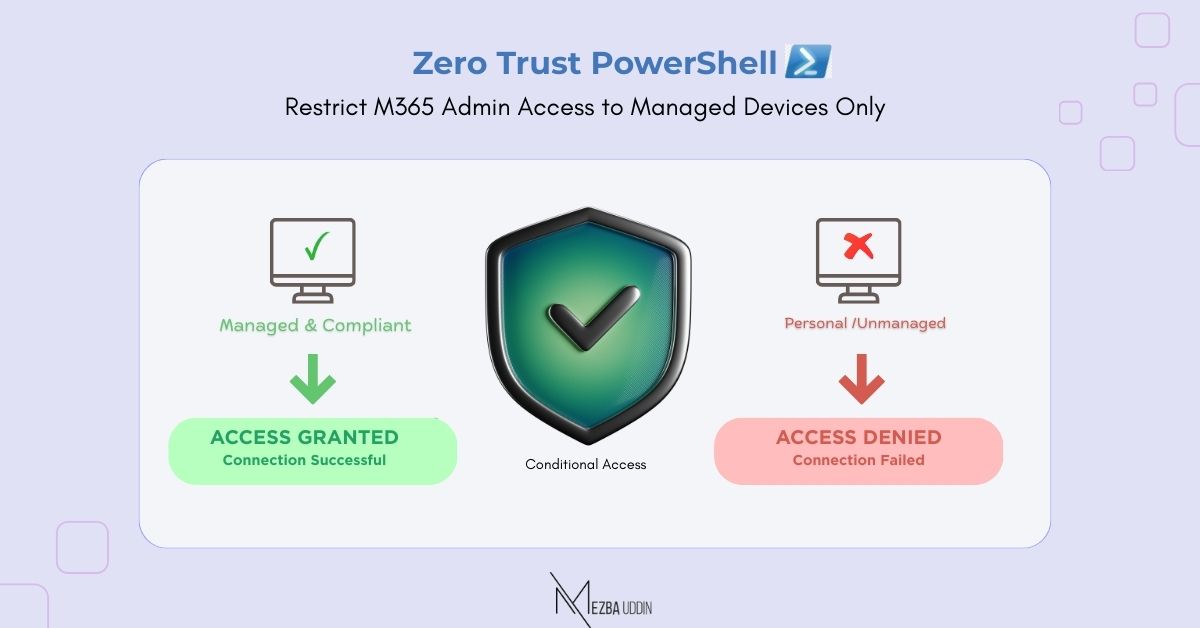
This guide demonstrates how to implement Zero Trust principles for PowerShell-based M365 administration using Microsoft Entra Conditional Access with device filters.
The Problem: Unrestricted PowerShell Access
Traditional M365 environments often allow administrative PowerShell connections from any device, anywhere. This creates several vulnerabilities:
- Unmanaged device access: Admins connecting from personal laptops or home computers.
- Geographic anomalies: Connections from unexpected locations
- Credential theft exposure: Compromised credentials used from attacker-controlled systems.
- Lack of visibility: Difficulty tracking which devices are being used for admin tasks.
- Compliance gaps: Failure to meet regulatory requirements for privileged access management.
Implementing Zero Trust Principles for PowerShell Access
Zero Trust operates on the principle of “never trust, always verify.” For PowerShell admin access, this means:
- Verify explicitly: Always authenticate and authorize based on all available data points.
- Least privilege access: Limit user access with just-in-time and just-enough-access.
- Assume breach: Minimize blast radius and segment access; verify end-to-end encryption.
Prerequisites:
Before implementing this solution, ensure you have:
- Microsoft Entra ID P1 or P2 licenses
- Microsoft Intune for device management (or other MDM solution)
- Administrative access to Microsoft Entra admin center
- Enrolled and compliant devices for testing
- Modern PowerShell modules (Azure AD, Exchange Online, Microsoft Graph)
How to Restrict M365 PowerShell Access to Managed Devices Using Conditional Access
1. Prepare Your Managed Devices
a) Enroll Devices in Intune
Ensure administrative devices are enrolled in Microsoft Intune:
# Check device enrollment status Get-MgDevice -Filter "displayName eq 'ADMIN-WORKSTATION-01'"
b) Create Device Compliance Policies
Navigate to Intune > Devices > Compliance policies and create a device compliance policy specifically for admin workstations with stricter requirements than standard users.
c) Mark Administrative Devices
Tag devices that will be used for PowerShell administration. You can use device extension attributes or create a device group:
- Device Group: Create a dynamic or assigned group in Entra ID:
-
- Name: “AdminWorkstations-PowerShell”
- Add all approved admin devices
- Extension Attribute: Use Microsoft Graph to set a custom extension attribute:
# Set extension attribute on device
$deviceId = "your-device-object-id"
$body = @{
"extensionAttributes" = @{
"extensionAttribute1" = "PowerShellAdmin"
}
}
Update-MgDevice -DeviceId $deviceId -BodyParameter $body
2. Create the Conditional Access Policy
- Sign in to Entra admin center.
- Go to Entra ID > Conditional Access > Policies
- Click + New policy
a) Configure Policy Basics
- Name:
Zero Trust - Block PowerShell from Unmanaged Devices - Assignments:
-
- Select “Select users and groups” -> Directory roles.
- Include: Choose your admin roles (Global Administrator, Exchange Administrator, SharePoint Administrator, etc.)
- Exclude: Emergency access accounts (break-glass accounts)
- Target Resources
-
- Select “Select resources”
- Include the following applications:
- Office 365 Exchange Online (PowerShell)
- Microsoft Graph PowerShell
- Azure Active Directory PowerShell
- Office 365 SharePoint Online
Search for “PowerShell” in the app picker to find relevant applications.
Important: Office 365 Exchange Online includes the Exchange Online PowerShell connection endpoint.
b) Configure Conditions
- Client apps:
-
- Configure: Yes
- Select: Mobile apps and desktop clients
- Check: Other clients (this captures PowerShell connections)
- Device platforms:
-
- Configure: Yes
- Include: Windows (or specific platforms you support)
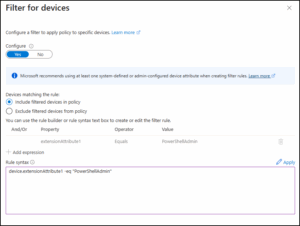
- Create Device Filter
This is the critical component that identifies approved admin devices. Navigate to Device Filter Configuration -> Filters for devices:
-
- Configure: Select Yes
- Devices matching the rule: Select Include filtered devices in policy
This configuration means the Conditional Access policy will apply TO (and allow access from) only the devices that match your filter criteria.
You have two options to create the filter:
Method 1: Use the Rule Builder
Click + Add expression to add a new rule
- Configure the expression:
- Property: Select
device.extensionAttribute1from dropdown - Operator: Select
Equals - Value: Enter
PowerShellAdmin
- Property: Select
- (Optional) Add additional expressions by clicking + Add expression again
- Use And logic to combine multiple conditions
Method 2: Use Rule Syntax (Advanced)
- Click Edit next to “Rule syntax” at the bottom of the dialog
- In the Rule syntax text box, enter:
device.extensionAttribute1 -eq "PowerShellAdmin"- Click Done to save the syntax
c) Configure Access Controls
Grant:
- Select Block access
This blocks PowerShell connections from devices that DON’T match your filter.
Alternative approach for staged rollout:
- Select Grant access
- Require: Device to be marked as compliant
- Require: Require approved client app (if applicable)
d) Enable Policy
- Select Report-only mode (for testing)
- After validation, change to On
Click Create to save the policy.
Testing the Results
On an approved administrative device (one that matches your device filter):
Connect-ExchangeOnline -UserPrincipalName admin@contoso.com Connect-MgGraph -Scopes "User.Read.All" Get-MgUser -Top 5
Expected result: Connection succeeds
On a personal or unmanaged device:
Connect-ExchangeOnline -UserPrincipalName admin@contoso.com
Expected result: Connection fails with authentication error related to Conditional Access
Best Practices
- Start with Report-Only Mode: Test policies before enforcement to avoid locking out admins
- Exclude Break-Glass Accounts: Always exclude emergency access accounts
- Use Groups for Scalability: Manage device assignments through groups rather than individual filters
- Document Everything: Maintain clear documentation of policies and approved devices
- Regular Reviews: Audit policies and device lists quarterly
- Layered Security: Combine with other controls (MFA, PIM, PAW)
Conclusion
Implementing Zero Trust principles for PowerShell administrative access is a critical step in securing your Microsoft 365 environment. By restricting PowerShell connections to managed, compliant devices through Conditional Access policies and device filters, you significantly reduce the attack surface and improve your security posture.
This approach ensures that even if administrative credentials are compromised, attackers cannot leverage them from unauthorized devices.