In complex Microsoft 365 environments, administrative actions carry significant risk. A misconfiguration or an accidental click during a routine task can trigger immediate and severe consequences, such as an unintentional remote device wipe or the deletion of critical enrollment records. These single points of failure directly contradict modern Zero Trust security models.
To mitigate this risk, organizations can implement the Multi-Admin Approval (MAA) feature for high-impact tasks within Intune. Often referred to as Dual Admin Control or the ‘Four-Eyes’ principle, MAA ensures that sensitive actions—such as a Device Wipe, Retire, or Delete must be reviewed and explicitly approved by a peer administrator before execution.
This is a critical governance layer that provides an indispensable audit trail and robust protection against human error. This guide details the steps necessary to configure and operationalize MAA for device actions in your environment.
Prerequisites:
Before configuring the MAA policy, two prerequisites must be correctly established.
Create the Dedicated Approver Security Group
This group will house all the administrators authorized to approve MAA requests.
- Sign in to the Microsoft Entra admin center.
- Navigate to Entra ID > Groups > All groups.
- Click + New group.
- Group type: Select Security.
- Group name: Give it a clear name (e.g.,
SG-Intune-MAA-Approvers). - Membership type: Select Assigned.
- Add the administrator accounts that will be authorized to approve the requests to the Members list.
- Click Create.
Link the Approver Group to an Intune Role
This step prevents the group from being “inadvertently pruned” from Intune’s data sync, ensuring it remains visible and functional for the MAA policy long-term.
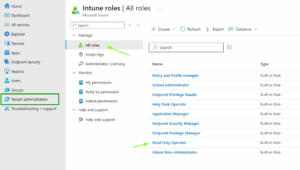
- Sign in to the Microsoft Intune admin center.
- Navigate to Tenant administration > Roles.
- Select an existing, low-impact role, such as the “Read Only Operator” role. (A custom role with zero permissions is also an excellent option).
- Select the Assignments tab, and then click + Assign.
- Give the assignment a name. Click Next.
- Admin Groups: Click + Select groups to include.
- Find and select your new Dedicated Approver Security Group (e.g.,
SG-Intune-MAA-Approvers). Click Select. - Click Next through the remaining settings (Scope groups and Scope tags).
- Review and click Create.
Creating the Multi-Admin Approval Access Policy
The Access Policy defines what action is protected and who is authorized to approve it. This step is performed by the initial administrator (the Requester).
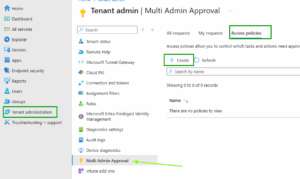
- Sign in to the Microsoft Intune admin center.
- Navigate to Tenant administration > Multi Admin Approval.
- Select the Access policies tab and click + Create.
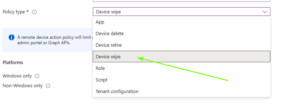
Define the Policy Scope
- Name: Enter a descriptive name.
- Profile type: Select Device wipe. Click Next.
- Select the Platforms to which this policy will apply.
- Click Next.
- On the Approvers page, click + Add groups.
- Select the Dedicated Approver Security Group you created in Step 1.
- Click Select, then click Next.
Submit the Policy for Approval
- Review the settings on the Review + submit for approval page.
- Provide a Business justification for creating the policy itself (e.g., “Implementing MAA as per security audit requirements to enforce separation of duties.”).
- Click Submit for approval.
Activating the Dual Role Policy in Intune
Since the policy creation is a security-impacting change, it requires approval before it can become active.
Review and Approve the Policy Creation (Approver Role)
- The Approver Admin signs in to the Microsoft Intune admin center.
- Navigate to Tenant administration > Multi Admin Approval > All requests.
- Locate and select the pending policy creation request.
- Add Approver notes.
- Click Approve request.
Complete and Activate the Policy (Requester Role)
- The Requester Admin signs back into the Intune admin center.
- Navigate to Tenant administration > Multi Admin Approval > My requests.
- The request status will show as Approved. Click the request.
- Click Complete.
Executing a Protected Device Action (The Workflow)
When an admin attempts a protected action, the workflow immediately triggers:
Initiating the Request (Requester Role)
- The Requester navigates to a device and selects a protected action (e.g., Device Wipe).
- A dialog box appears, showing the MAA requirement.
- The Requester enters a mandatory Business justification for the device action.
- The Requester clicks Submit for approval.
The device action is halted. The request is visible in the My requests tab with the status Needs approval.
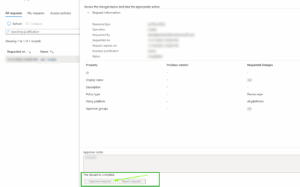
Reviewing and Approving the Action (Approver Role)
- The Approver signs in and navigates to Tenant administration > Multi Admin Approval > Received requests.
- They review the device, the action type, and the Requester’s justification.
- They add Approver notes (e.g., “Verified user termination date, proceeding with device retire.”).
- They click Approve request.
The request status changes to Approved.
Finalizing and Executing the Action (Requester Role)
- The Requester returns to My requests.
- The request status is Approved. Click the request.
- Click Complete.
Intune executes the device action. The complete workflow is recorded in the audit logs.
Conclusion:
By implementing Multiple Administrator Approval, you establish a true governance framework that secures your environment against human error and malicious intent. Every critical device action is now backed by an auditable workflow that confirms who requested it and who provided oversight. This is a non-negotiable step toward modern, compliant security.